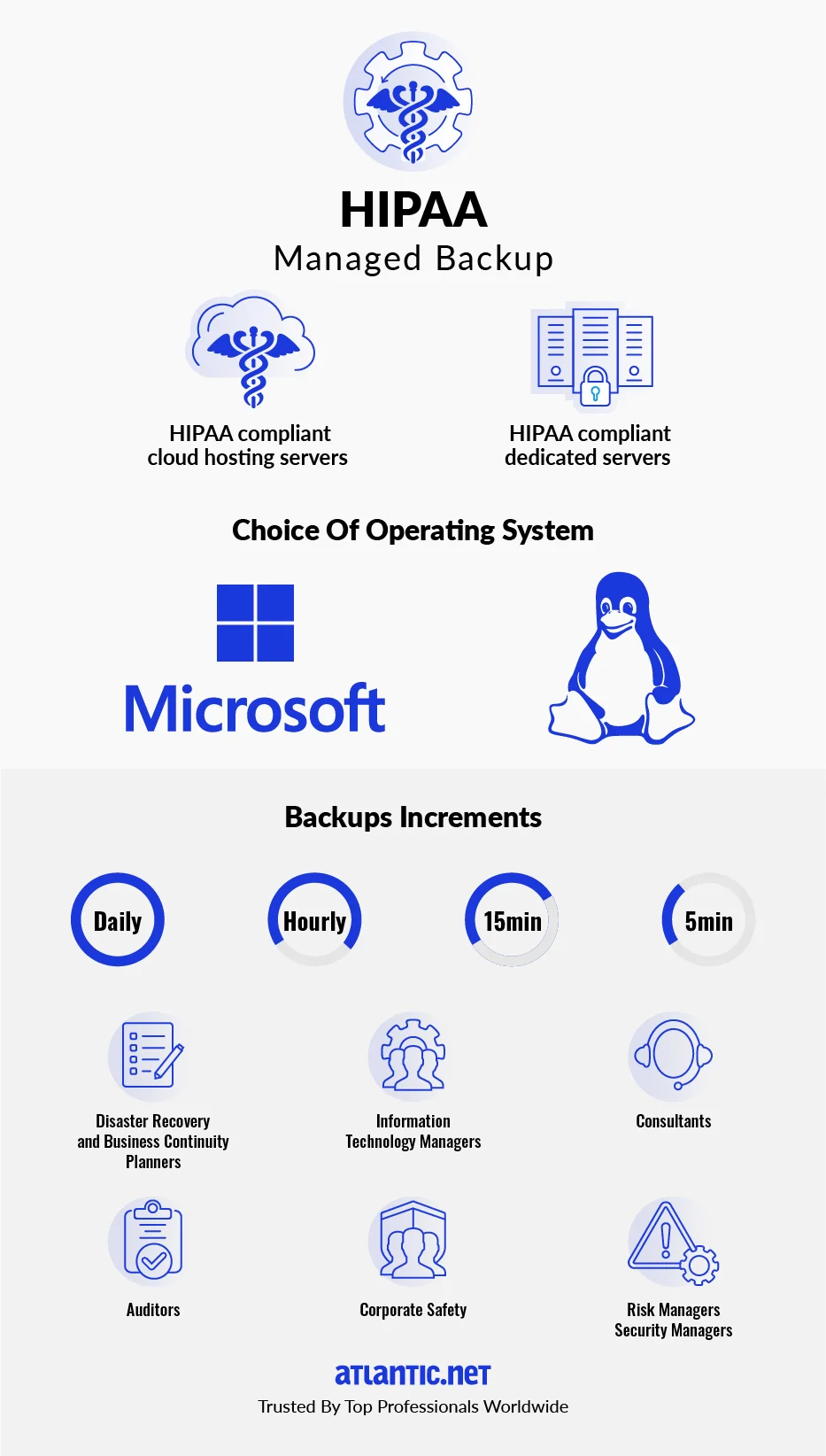
Disaster Recovery and Business Continuity for HIPAA Compliance
At Atlantic.Net, we've spent the last three decades preparing for the next disaster by combining experience, expertise, and world-class hosting infrastructure to provide the most secure HIPAA Disaster Recovery hosting solution ‐ designed for uninterrupted business continuity.
To minimize risk and help you get back to business quickly, Atlantic.Net offers off-site backup and replication of your mission-critical data away from the primary facility. This ensures smooth data recovery in the event of a local outage or regional disaster. Our Disaster Recovery solutions are ideal for privacy, security, and compliance work that requires adherence to the strictest government regulations.