Regardless of the application, any efforts to maintain HIPAA compliance are directed at the same core concern – safeguarding the confidentiality, integrity, and availability of electronic protected health information (ePHI). The technological setup will vary considerably based on the size and complexity of the organization.
Since the IT needs of organizations are so diverse, HIPAA compliance is not a cookie-cutter challenge, so cookie-cutter solutions are insufficient. That customization for each individual client’s setup is the core of what a strong HIPAA-compliant provider can offer. Regardless of that case-by-case aspect to meeting compliance (particularly the Security Rule), it still helps to look at typical setups for various types of ecosystems. Below, we look at a sample HIPAA-compliant WordPress configuration and then discuss some of its key components.
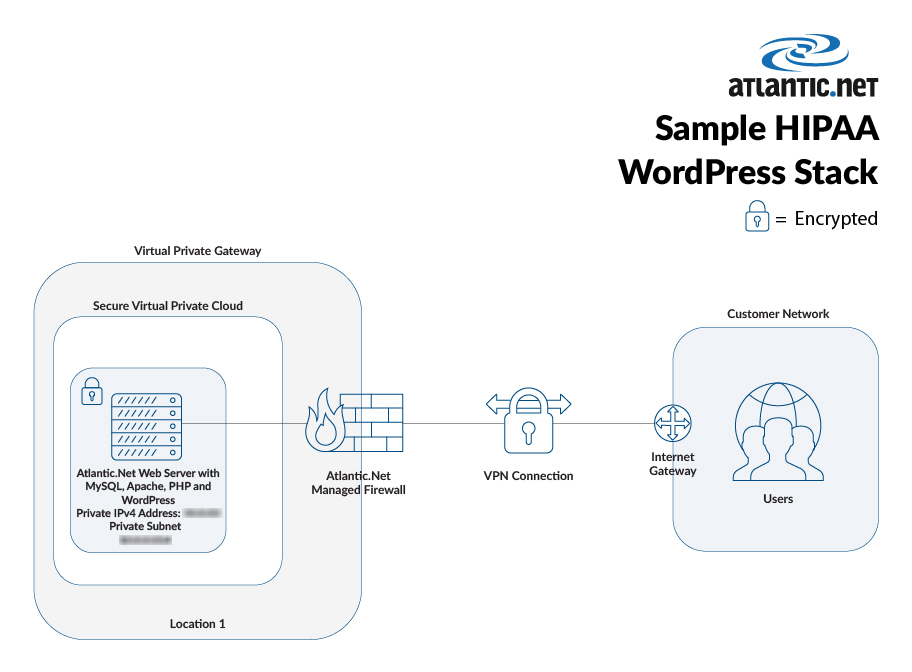
Sample HIPAA WordPress Setup
The technologies of a typical HIPAA-compliant WordPress setup for a smaller healthcare provider or business associate might be the following:
- 2.4 Gigabit (Gb) cloud server
- Server management
- Managed firewall
- VPN client with a firewall appliance for every 10 VPN users
- Managed intrusion prevention system
- Continuous data protection (CDP) backup with 30 days retention
- 10 TB of monthly data transfer
- Managed anti-malware solution
- Managed network security solution
- Managed system security solution
Hardened OS & Software
Hardening systems is critically important for HIPAA compliance. The servers that support your WordPress environment must be optimized for security. Whether you are working with Windows or Linux, you want to follow best practices such as:
- Updating to supported operating systems (keeping problematic devices off the network, air-gapping, or otherwise controlling that access)
- Configuring and patching your server database
- Consistently patching third-party software
- Scanning for open shares
- Disabling services
- Configuring host-based firewalls
- Separating disk partitions
- Managing file integrity
Business Associate Agreement
As with any other environment in which a third party will handle health data on your behalf, a WordPress setup requires a business associate agreement (BAA). The BAA must follow the guidelines established by the HIPAA Final Omnibus Rule, which was mandated by the Health Information Technology for Economic and Clinical Health (HITECH) Act. The Omnibus Rule altered how organizations maintain compliance with the Privacy Rule. The Privacy Rule stipulates that covered entities (healthcare plans, providers, and data clearinghouses) must confirm and validate that every service provider with which they work (called business associates) will safeguard health records as directed by the HHS Department. A BAA will help set the expectations of your relationship and the responsibilities for ePHI at all points and in all forms. Note that the BAA is complemented by the SLA, which provides business expectations related to meeting the needs of compliance, such as an uptime guarantee that is not only a business expectation, but also meets the HIPAA availability requirements.
Intrusion Prevention
To monitor your network for any cybercriminal activity, you need an intrusion prevention system (IPS), also called an intrusion detection prevention system (IDPS). You could see issues, including security policy violations by insiders and security threats from outsiders. Anything that looks unusual gets blocked by the IPS, with logging and reporting. These systems must be properly configured and managed.
Managed Firewall
It is important to have a fully managed firewall so that your perimeter is protected against any parties that might want to enter against your wishes. The managed firewall will give you log monitoring 24/7, oversight that many organizations cannot achieve internally. Within a managed firewall setting, you also get routine health checks of your equipment. Managed service providers that offer this service and have a strong healthcare background will be especially well-prepared for a data breach.
Continuous Data Protection Backup
It is important to HIPAA compliance that your backups are extremely high-grade – keeping in mind that a backup is both important to maintaining availability and to maintaining security for phishing ransomware scenarios in which you might otherwise not have current records. A storage technology that gauges alterations within data systems in real time, creates data restore points, and enables efficient recovery from any incidents, continuous data protection (CDP) can additionally log any changes made to data. Also called real-time backup, storage convergence, and continuous backup, CDP is used in remote backup settings and is facilitated by wide area networks that are outfitted for automatic connection failure and recovery.
Encryption
Encryption is not mandatory under HIPAA – technically. It is denoted within the guidelines as an “addressable” measure. The fact is that you need full encryption, an alternative that accomplishes that same confidentiality protection, or a reasonable explanation for why you did not secure the environment. An organization might be able to justify skipping encryption for a firewalled internal messaging system, for instance, but not for a typical WordPress setup.
Achieving HIPAA Compliance within WordPress
HIPAA compliance is not only about setting up systems, but also fundamentally about maintaining an environment that properly safeguards patient data. That ongoing safety is probably the biggest reason to go with a managed services provider for a WordPress project. Make sure that MSP has strong healthcare experience. At Atlantic.Net, our HIPAA Hosting Solutions have been audited by a qualified independent third-party auditing firm, demonstrating our commitment to providing the best IT security and compliance solutions. See our WordPress HIPAA hosting plans.
Read More About HIPAA Compliant Hosting
- HIPAA Compliant Hosting
- How to Make a HIPAA-Compliant Website
- HIPAA Compliant Server Case Study
- Best Practice for a HIPAA WordPress Website
- HIPAA Compliant Data Center
- HIPAA Compliant WordPress Hosting
* This post is for informational purposes only and does not constitute professional, legal, financial, or technical advice. Each situation is unique and may require guidance from a qualified professional.
Readers should conduct their own due diligence before making any decisions.