Table of Contents
- HIPAA-Compliant Hosting Services Checklist
- First-Class Healthcare HIPAA Hosting vs. Standard Hosting: What’s the Difference?
- Responsibilities for Safeguarding Electronic Protected Health Information Are Defined by the HIPAA Final Rule
- What Is HITECH?
- What Are Examples of Covered Entities and Business Associates?
- HIPAA Violations Can Result in Jail Time
- Top 11 HIPAA Fines by Settlement 2014-2024
- The HHS Audit Program
- What Is the HIPAA Security Rule?
What should you look for in a reliable HIPAA-compliant hosting provider? Healthcare hosting providers must comply with HIPAA, the Health Insurance Portability and Accountability Act of 1996, which requires them to safeguard and securely store patient records and other protected health information (PHI). Modern HIPAA hosting requirements now emphasize continuous monitoring, risk analysis, and layered security protections to safeguard sensitive data across hybrid and cloud environments. When evaluating HIPAA-compliant hosting providers, it is important to understand how well the provider is prepared for HIPAA audits and whether their infrastructure, policies, and operational procedures support ongoing compliance.
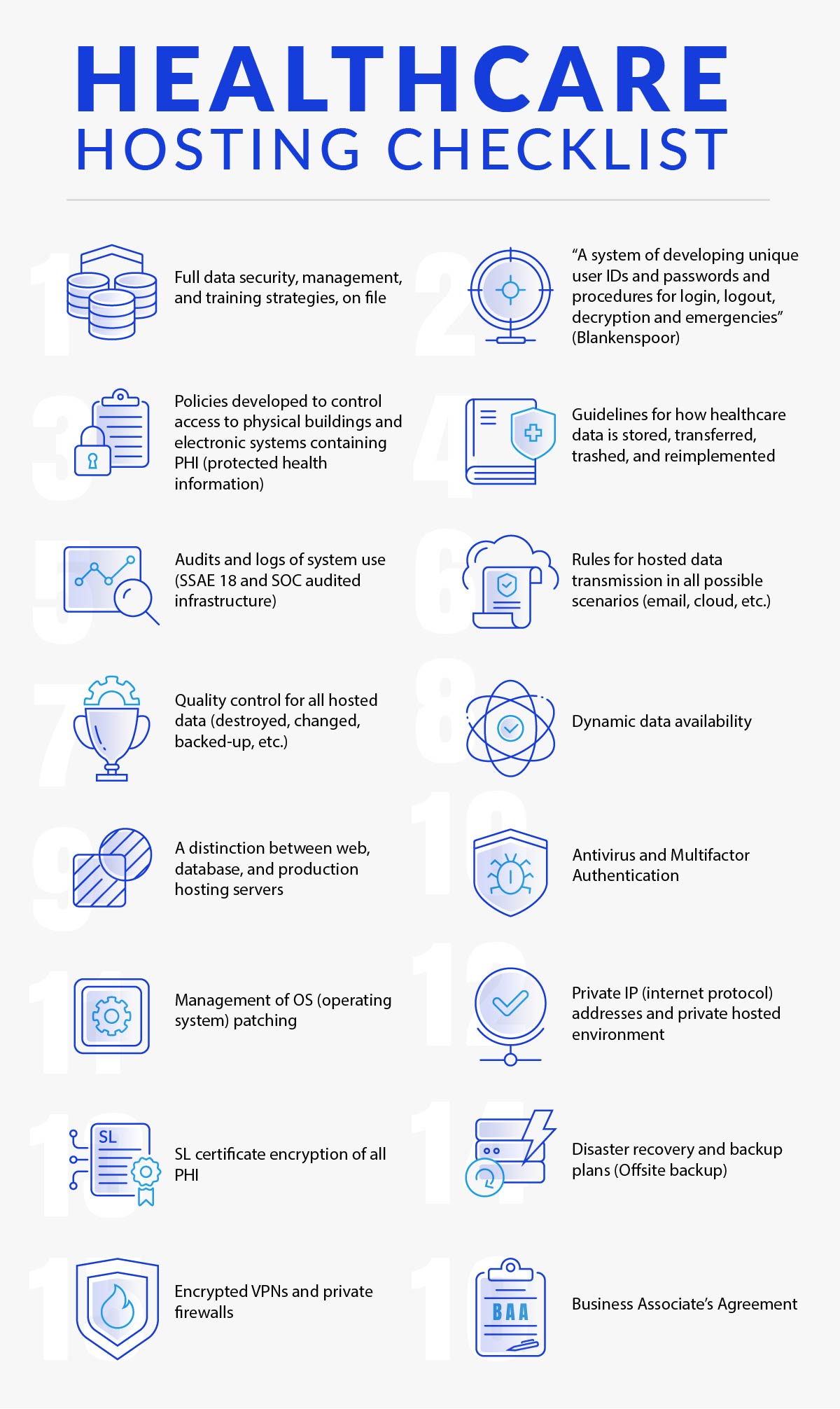
HIPAA-Compliant Hosting Services Checklist
The first step in ensuring HIPAA compliance from your web hosting provider is to review HIPAA-compliant hosting requirements. The following 16-point HIPAA Hosting Checklist covers fundamental considerations. This checklist should also be aligned with current hipaa guidelines, including implementing security measures that address evolving security risks and threat vectors. While it provides a useful starting point, it should not be considered a complete substitute for a full HIPAA compliance assessment:
- Documented strategies for data security, access management, and staff training to reduce security incidents
- A system for creating unique user IDs and passwords, along with procedures for login, logout, decryption, and emergency access (Blankenspoor)
- Policies governing access to physical facilities and electronic systems that store or process protected health information (PHI)
- Clear procedures for how healthcare data is stored, transferred, disposed of, and restored when necessary
- Auditing, logging, and monitoring systems to track data access and detect unauthorized activity
- Rules governing hosted data transmission across all scenarios (email, cloud platforms, and other communication channels)
- Quality control measures for hosted data, including deletion, modification, and backup management
- Reliable data availability to ensure systems remain accessible when required
- Separation between web servers, database servers, and production hosting environments
- Antivirus protection and multi-factor authentication (MFA)
- Ongoing management and patching of the operating system (OS)
- Use of private IP (Internet Protocol) addresses within a secured hosting environment
- Strong data encryption protocols for data at rest and in transit
- Disaster recovery and backup strategies, including offsite backups
- Network security controls such as firewalls, intrusion detection, and VPN protections
- A signed Business Associate Agreement (BAA)
Click here to learn more about HIPAA hosting.

First-Class Healthcare HIPAA Hosting vs. Standard Hosting: What’s the Difference?
One of the fundamental realities of the Internet is that applications and services ultimately run on physical or virtual machines, either hosted internally or provided by a third-party service. For healthcare organizations that prefer not to maintain servers in their own data centers, HIPAA-compliant web hosting is a practical alternative.
Not all hosting environments provide the same level of security or operational controls. HIPAA compliant servers are specifically designed with privacy and security protections that align with regulatory expectations, unlike standard hosting environments. Security standards and oversight can vary widely across providers; formal guidelines were established to ensure consistent protection of healthcare data. These standards are defined by the U.S. Department of Health and Human Services (HHS) under the Health Insurance Portability and Accountability Act of 1996 (HIPAA). As a result, organizations responsible for handling healthcare records must rely on HIPAA-compliant hosting environments, often referred to simply as HIPAA hosting, rather than standard web hosting services.
“HIPAA recognizes all health care providers and their business associates as covered entities (CEs) and makes them responsible to safeguard the privacy and security of identifying information.” “Some CEs, particularly smaller sized CEs, don’t have the resources necessary to implement a system to handle and safeguard health data on their own, so they rely upon the services of HIPAA hosting.”
Jacco Blankenspoor of HIPAA HQ[i]
Any hosting provider can offer HIPAA-compliant hosting services based on its own interpretation and implementation of healthcare regulatory requirements. Because there is no formal certification, organizations must evaluate providers based on their ability to implement specific security measures and maintain compliance over time. In other words, there is no official federal certification program that formally designates a hosting provider as “HIPAA-certified.” Because of this, the responsibility for evaluating the quality and reliability of the HIPAA hosting infrastructure supporting any hosted service ultimately falls on the healthcare organizations that use those services. In practice, this means healthcare-covered entities must perform their own due diligence to confirm that the hosting environment they rely on meets HIPAA compliance expectations.
Similarly, the federal government does not officially recognize any specific third-party certification bodies for HIPAA hosting providers. This has allowed a competitive ecosystem to develop where providers demonstrate credibility through independent audits and industry-recognized compliance frameworks. At the same time, it also means that healthcare organizations must carefully evaluate the credibility of the auditing or certification body involved, as well as understand exactly which controls, safeguards, and review processes are included in that provider’s HIPAA compliance assessment.

Responsibilities for Safeguarding Electronic Protected Health Information Are Defined by the HIPAA Final Rule
Given the broader lack of formal standards defining what specifically qualifies as “HIPAA-compliant hosting,” there is at least one important advantage for covered entities. Business associates (BAs), including HIPAA-compliant web hosting providers, are required to safeguard data in much the same way covered entities do. This includes implementing security measures aligned with the HIPAA Security Rule, which defines administrative, physical security, and technical safeguards required to protect patient data. Covered entities include healthcare providers, health plans, and healthcare clearinghouses. This shared responsibility became firmly established following the implementation of the Omnibus HIPAA Final Rule (commonly referred to as the Final Rule or Omnibus Rule), which took effect on March 26, 2013.
Under this rule, business associates that create, receive, maintain, or transmit electronic protected health information (ePHI) are directly accountable for complying with applicable HIPAA security and privacy requirements, rather than relying solely on contractual obligations with covered entities. As a result, hosting providers that support healthcare workloads must ensure that their infrastructure, administrative policies, and technical safeguards align with HIPAA requirements when handling sensitive healthcare data.
Following passage of the rule, business associates “are liable for PHI uses and disclosures and HIPAA Security Rule compliance.” “Additionally, BAs with their subcontractors, while BAs – not covered entities – are also now responsible for responding to any noncompliant subcontractors.”
Elizabeth Snell of HealthIT Security[ii]
Health and Human Services also established a process for randomly selecting covered entities for HIPAA compliance audits. These audits evaluate whether organizations are properly adhering to the core HIPAA requirements, including the Security Rule, the Privacy Rule, and the Breach Notification Rule. These audits now heavily evaluate risk analysis processes, breach notification procedures, and how organizations respond to security incidents. The purpose of these audits is to assess how healthcare organizations and their partners protect electronic protected health information (ePHI) and whether appropriate safeguards and reporting procedures are in place.

What Is HITECH?
HITECH (the Health Information Technology for Economic and Clinical Health Act of 2009) was introduced to support the transition from paper-based medical records to digital health data while maintaining strong safeguards around patient information. HITECH also strengthened enforcement of the HIPAA Breach Notification Rule, requiring faster and more transparent reporting of data breaches involving sensitive data. While HITECH outlines how electronic health records can be shared and managed within modern healthcare systems, HIPAA establishes the responsibility for protecting that data. Under HIPAA, any organization or individual that accesses, stores, or processes electronic protected health information (ePHI) is responsible for maintaining its security.
Specific security controls are not rigidly prescribed in every situation. Instead, organizations must conduct regular risk analysis and implement security measures appropriate to their size, complexity, and risk exposure. As Blankenspoor noted, “[T]he HHS allows entities to implement their own chosen methods.” At the same time, established industry best practices play an important role. Healthcare organizations are generally expected to follow widely accepted security approaches or demonstrate that the alternative systems they implement provide an equivalent or stronger level of protection for sensitive healthcare data.

What Are Examples of Covered Entities and Business Associates?
The term “covered entity” specifically includes all healthcare providers, health plans, and healthcare clearinghouses operating in the United States. Like their business associates who are engaged through a Business Associate Agreement (BAA) as required under HIPAA, covered entities must independently comply with all applicable HIPAA regulations.
A Business Associate Agreement defines the responsibilities for protecting patient data between the covered entity and the business associate. It also outlines breach notification procedures and responsibilities under the HIPAA breach notification rule. This agreement establishes how protected health information (PHI) must be handled, secured, and reported in the event of an incident. For this reason, a Business Associate Agreement is an essential requirement when selecting a HIPAA-compliant hosting provider.
In general, covered entities are healthcare organizations and agencies whose core operations involve the use or management of protected health information. A business associate, on the other hand, is an organization that performs services or functions on behalf of a covered entity and may require access to PHI in order to do so. Business associates include hosting providers, SaaS vendors, and any organization handling patient data on behalf of healthcare services. HIPAA-compliant hosting providers are one example of a business associate under HIPAA. Other examples that typically require a Business Associate Agreement include medical billing providers and document shredding companies that handle sensitive healthcare records.

HIPAA Violations Can Result in Jail Time
As with any regulatory requirement, some organizations may consider avoiding the investment required to meet HIPAA compliance standards. However, failure to implement adequate data security and security protections can result in severe financial and legal consequences. Under the law, intentionally failing to comply with HIPAA requirements is referred to as willful neglect. Financial penalties for this type of violation generally range from $10,000 to $50,000 per incident, with an annual maximum of $1.5 million per organization. Organizations that fail to address known security risks or ignore required safeguards may face higher penalties and increased scrutiny. In severe cases, particularly where willful neglect results in the exposure of sensitive patient data, criminal penalties, including potential jail time, may also apply.
Not all violations are categorized as willful neglect. In some cases, they may fall under the definition of reasonable cause. These situations typically involve circumstances where safeguards were insufficient or procedures were not properly followed, leading to the exposure of protected health information. For example, incidents involving the exposure of 500 or more individual medical records can result in fines ranging from $100 to $50,000 per violation. However, violations categorized under reasonable cause are generally not associated with criminal penalties or jail time.

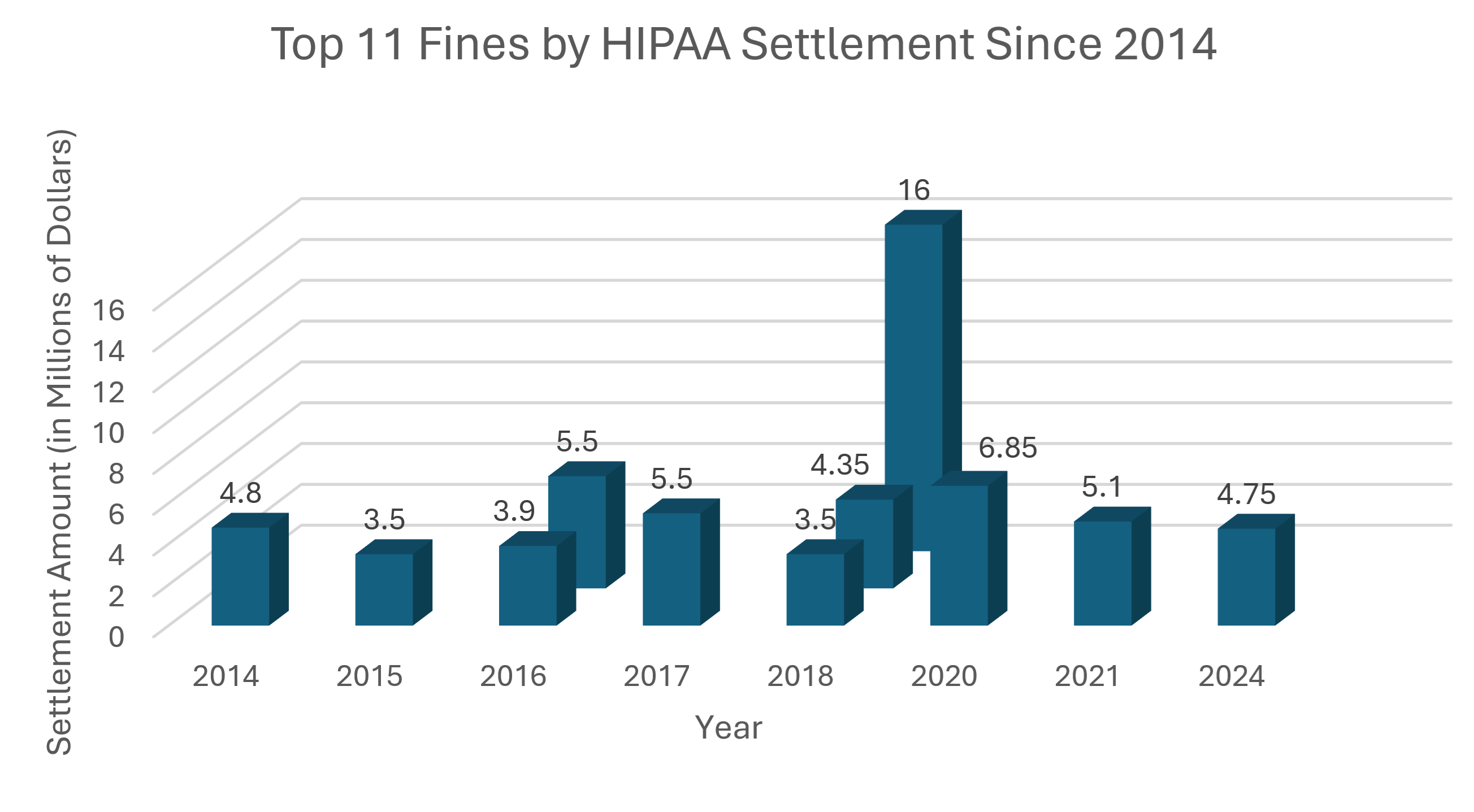
Top 11 HIPAA Fines by Settlement 2014-2024
Sources: Compliancy Group and the HIPAA Journal.
It is worth noting that 6 of the 11 largest HIPAA settlements occurred in 2018, 2020, 2021, or 2024. These cases highlight how enforcement activity has intensified in recent years as regulators continue to scrutinize how healthcare organizations and their partners handle sensitive patient data. Recent enforcement trends show a growing focus on access management failures, weak network security, and inadequate breach response processes. The largest HIPAA settlement to date occurred in 2018, when Anthem agreed to pay a $16,000,000 fine following a major data breach that exposed the protected health information of millions of individuals.

The HHS Audit Program
The random audit initiative began with a pilot program that involved 113 companies and organizations across the healthcare sector. Today, audits increasingly assess how organizations implement security measures, manage data access, and document compliance with HIPAA guidelines. This initial phase enabled the U.S. Department of Health and Human Services (HHS) to better evaluate how organizations were approaching HIPAA compliance and identify both effective practices and common areas of noncompliance. The insights gathered during the pilot program helped shape how HHS conducts compliance reviews and how enforcement actions are applied when violations occur.
“[Atlantic.Net’s] financial strength and proven track record are something we view with great confidence.”
Joseph Nompleggi, Vice President, Complete Healthcare Solutions

What Is the HIPAA Security Rule?
The Privacy Rule focuses on safeguarding patient health information, including electronic health records. The Security Rule is particularly relevant in the context of HIPAA-compliant hosting because it establishes more detailed requirements for the storage, protection, and transmission of health data, especially for electronic protected health information (ePHI). The security rule defines how organizations must protect electronic PHI through administrative, physical security, and technical controls.
The HIPAA Security Rule is organized into three primary safeguard categories: Administrative Safeguards, Physical Safeguards, and Technical Safeguards. These safeguards collectively ensure strong data encryption, access management, and network security across healthcare systems. Over time, the Security Rule has become increasingly important as healthcare organizations rely more heavily on digital systems, cloud infrastructure, and modern data management technologies.
As Blankenspoor explains, “The same standards for the privacy and confidentiality of healthcare data apply to PHI and ePHI, but the processes used to keep data private are much more complex and technical for electronic data files and ePHI than they are for paper files.”(iii)
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) required the Secretary of the U.S. Department of Health and Human Services (HHS) to establish regulations designed to protect the privacy and security of certain health information. To meet this requirement, HHS introduced the HIPAA Privacy Rule and the HIPAA Security Rule, now commonly known. The Privacy Rule, formally known as the Standards for Privacy of Individually Identifiable Health Information, establishes national standards for protecting certain types of health information. The Security Rule, known as the Security Standards for the Protection of Electronic Protected Health Information, establishes a national framework for securing health information that is stored or transmitted in electronic form.
The Security Rule builds upon the protections defined in the Privacy Rule by addressing both technical and non-technical safeguards that covered entities must implement to secure individuals’ electronic protected health information (ePHI). Within HHS, the Office for Civil Rights (OCR) is responsible for enforcing the Privacy and Security Rules through compliance oversight, voluntary resolution efforts, and civil monetary penalties when violations occur.
How Can You Get Healthcare Hosting That’s HIPAA-Compliant Right Now?
Are you evaluating HIPAA-compliant cloud hosting and storage providers for your business, but not sure where to start? Atlantic.Net’s HIPAA-compliant hosting is HIPAA-Audited, HITECH-Audited, and backed by SSAE 18 (formerly SSAE 16) SOC 1 Type II and SOC 2 Type I reports. We can assist with healthcare hosting, from design to deployment, so you can continue to focus on your core business. Contact us today for a free healthcare hosting consultation
[i] HIPAA compliant hosting explained
[ii] http://healthitsecurity.com
[iii] laws regulations
Updated 25th March 2026
Related Guides:
Related Products:
* This post is for informational purposes only and does not constitute professional, legal, financial, or technical advice. Each situation is unique and may require guidance from a qualified professional.
Readers should conduct their own due diligence before making any decisions.