Verified and Tested 05/12/15
Introduction
With any server, the primary goal should always be security. Many users are victims of malicious infiltrations on their servers due to the lack of security boundaries established from the beginning. Let us begin on the right path by laying our foundation with security. This how-to will help you with your initial setup on Fedora 21 so that you can successfully secure your server while giving you peace of mind knowing your server is protected.
What Do You Need?
You need a Fedora 21 server configured with a static IP address. If you do not have a server already, consider a cost-effective server from Atlantic.Net and be up in 30 seconds.
Server Preparation
To get started, log in to your Fedora 21 server via SSH or the VNC Console located here. Atlantic.Net Cloud servers are set up as minimal installations to avoid having unnecessary packages from being installed and never used. If some software packages that you’re used to using aren’t installed by default, feel free to install them as needed.
Let’s make sure that your server is fully up-to-date.
yum update
We can continue the process and secure your server with the server up-to-date.
Update the Fedora 21 Root Password
By default, your Atlantic.Net servers are automatically set with secure passwords. However, we still recommend updating your password after creating your server and every 60-90 days after that to ensure it remains secure. A minimum of 8 characters, including lowercase, uppercase, and numbers, are recommended to increase the level of security.
Type the following command to activate your request and follow the on-screen instructions to update/confirm your root password:
passwd
Create a new user with sudo privileges
After successfully updating your password, it’s recommended that you create a new user with sudo/root permissions. Since the typical admin user for many Linux Operating Systems like Fedora 21 is “root,” we will make a new admin user that will be used for day-to-day administration tasks. Creating a new user with root permissions will increase the security of the way your server is accessed. Individuals looking to target your system will target the root user because it’s known to be the default admin account. By creating a new user with sudo/root permissions and disabling the root user, you are increasing security by using a user that isn’t already publicly known.
Type the following command to create your new user replacing “user1” with your username, and confirm.
adduser user1
Create a password for that user by typing the following command to activate your request and following the on-screen instructions to update/confirm your “user1” password:
passwd user1
Once you have created a new user and created the password for that user, it is time to add the user to the sudo wheel group. In Fedora 21, once you add them to the sudo wheel group, they are automatically assigned sudo/root permissions. Run the following command to add the user to the sudo wheel group.
gpasswd -a user1 wheel
Finally, when you have created the user with sudo/root permissions, you can exit your session and log back in with your “user1” to verify the changes made. Alternatively, you can run the following command and switch users from root to “user1,” which will ask you for that user’s password.
su - user1
Configure SSH Access
Port 22 is the default port for remote connections via SSH in Linux systems. By changing the ssh port, you will increase the security of your server in preventing brute force attacks and unwanted users from reaching your server using the default port. For this tutorial, we will use Port 5022 as an example.
Open your SSH Configuration file, find the Port line, remove the # and change 22 number to your Custom port. Save and exit.
sudo vi /etc/ssh/sshd_config
#Port 22 Port 5022
For your system to update the settings from the SSH Configuration file, we must restart the sshd service.
sudo systemctl restart sshd.service
SSH has now been configured to use Port 5022, and if you attempt to login using Port 22, your login will fail. However, do not exit your session as we need to configure the custom port on the firewalls configuration part first, which we will configure in the upcoming steps.
Limit Root Access
Since we’ve created a new user with root permissions and made a custom ssh port, there’s no need to keep the actual root user available and vulnerable over SSH on your server. Let us restrict the root user’s access to the local server and grant permission to the new user over SSH only.
Open the SSH Configuration file, find the PermitRootLogin line, remove the # and change it from yes to no.
sudo vi /etc/ssh/sshd_config
#PermitRootLogin yes PermitRootLogin no
For your system to update the new settings in the SSH Configuration file, we must restart the sshd service.
sudo systemctl restart sshd.service
Note: You will now have the root user disabled in making those changes, so you must log in to your server with the “user1” that you created. However, do not exit your session. We must configure the custom port on the firewall in the upcoming steps.
Create a Private SSH Key
Private/Public SSH Keys are great additional features that increase security in a server’s method. However, it takes a bit more effort to set up. The question is, Is your server worth the extra security? If you want to implement the following security features, you can continue with the next steps. Let us proceed and generate the SSH Key.
ssh-keygen
If you want to change the location where the SSH Key will be saved, you can specify it here. However, the default location where it’s stored should be OK. Press enter when prompted with the following question, then enter a passphrase, unless you don’t want one.
Enter file in which to save the key (/home/user1/.ssh/id_rsa):
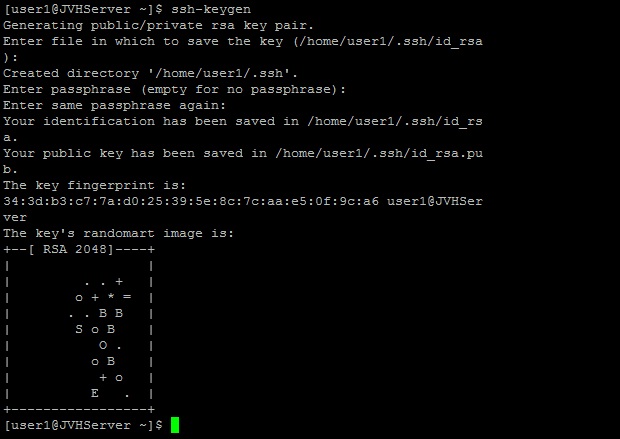
This is the default webpage when installing SSH Keys on a Fedora21 server
Configuring the SSH Key is crucial. We must copy the entire key string to a Word/ Notepad Document. The Key can be viewed in the following location with the cat command.
cat ~/.ssh/id_rsa.pub
Copy the SSH key, beginning with ssh-rsa and ending with user1@yourserver, into a Word/ Notepad document to add it to the config file later on.
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDbFd5OZFm8qDh21f28igkEVVb0rwkvyvxpH+LX9FBIgLfXTYZRz8PhCUi6NtugZMJ3F9vwq4Cq3zTYuwqhdb4Nt8z8MiS6sKX8JpgLyKreEwaxfK9IKBskyAkpln7zc7bHVCYsTJsvr/1B7kTvX4jIa0/EJQS7xvCTGdMDOD+Ux7bGJiA8ohc4DfELfJnlcURfNwB3PZ5ukdoul7/+yeabRsj18rc0yZfJ3/MgaipdSTwK/2mpaR0xlKGQhj47FsERKu6rztBL5lIQXWWZK71L8O2aprgsBBP+G2lKVKNNXeBfd+4Kx+4D980mWZlEdZ8KfgOZqCMXF3Jfjqcpvf0D user1@JVHServer
Once the SSH Key is stored safely, the directory for the SSH Keys needs limited permissions that only the owner can read, write and execute the file.
chmod 700 .ssh
Within the SSH directory, a file containing the SSH Key must be added, simply using your editor (in this case VI) the following location:
vi .ssh/authorized_keys
Paste the SSH Key, then save and exit using the VI format.
Finally, we have to limit the permissions of the authorized_keys file that we just created so only the owner can read and write.
chmod 600 .ssh/authorized_keys
We could now verify that the key is working by closing the session and typing user1@YOUR.IP.ADD.RESS or your server’s hostname in your SSH console. Furthermore, you can click “here” to see our How To Generate and Use SSH Keys article for more information.
Basic Firewall Rules
By default, your Atlantic.Net’s Fedora 21 Server is loaded with a default firewall named firewalld that uses the firewall-cmd to configure its rules. We must first start the Firewall service with the following:
sudo systemctl start firewalld
Next, we’re going to add a rule to allow the custom SSH Port 5022 that was created earlier to access the server publicly. At the same time, we will remove the previous default rule allowing SSH access on TCP/22.
sudo firewall-cmd --permanent --add-port=5022/tcp
sudo firewall-cmd --permanent --remove-service=ssh
If you have a web server, you may want to allow the following rules to access your sites over the internet.
sudo firewall-cmd --permanent --add-service=http sudo firewall-cmd --permanent --add-service=https
You can use this for similar rules related to any systems you want to be publicly accessible. This test server is set up to host a website and email services, so in addition to the updated SSH and HTTP(S) rules, additional rules for secure POP3, IMAP, and SMTP have been added.
sudo firewall-cmd --permanent --add-service=pop3s sudo firewall-cmd --permanent --add-service=imaps sudo firewall-cmd --permanent --add-service=smtp
For Firewalld to accept those settings, you must restart the firewall.
sudo firewall-cmd --reload
Your settings will have been saved, and you are ready to proceed.
To verify all the services/ports that are available, run the following:
sudo firewall-cmd --permanent --list-all
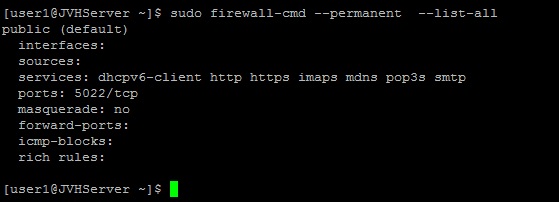
This is the default webpage after completing the Firewalld rules on a Fedora21server
NTP Time Sync
The NTP (Network Time Protocol) is used to synchronize the time and date of computers over the network to remain accurate and up to date. Let us begin by installing the NTP(If it hasn’t been installed) and configuring the service to synchronize with their servers.
sudo yum install ntp
Once the NTP service is installed, we need to ensure that the service is ON.
sudo systemctl start ntpd
Now that the service has started, let’s enable the NTP server to update the server’s time from the NTP server constantly.
sudo systemctl enable ntpd
Add Swap File
A Swap file is simply a tiny amount of space created on a server hard drive to simulate RAM. If the server is running low on memory, it will look at the hard drive and ease the load tricking the system into thinking it has more memory. We will set up the swap file on the hard drive to increase the server’s performance just a little bit more.
Begin by checking your resources to make sure we can add the file. When you run the following command, you will see the percentage space on your Hard drive that is currently being used.
df -h
When creating a Swap file, you usually want to add half of your existing RAM up to 4GB(If you have 1GB of actual Ram, you add a 512MB file). In this part, I will be adding a 512MB swap file to the drive. The way that this is calculated is by 1024 x 512MB = 524288 block size.
sudo dd if=/dev/zero of=/swapfile bs=1024 count=524288
Now that we have added a swap file, an area needs to be created to proceed.
sudo mkswap /swapfile
With the Swap file created and the Swap file, area added we could go ahead and add permissions to the file so that only the owner can read and write.
sudo chown root:root /swapfile sudo chmod 0600 /swapfile
Now that the swap file has the appropriate permissions, we can go ahead and activate it.
sudo swapon /swapfile
You can verify your newly added Swap file with the following.
sudo swapon -s
To make the Swap file always active even after a reboot, we must configure it accordingly.
sudo vi /etc/fstab
Paste the following command at the bottom of the file, save your work, and exit.
/swapfile swap swap defaults 0 0
Finally, verify if your swapfile is activated by typing the following command:
free -m
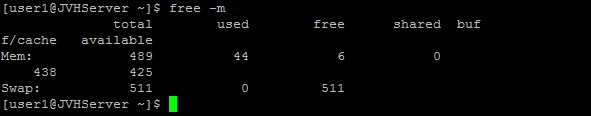
This is the default page after creating a Swap File on a Fedora21 Server
What Next?
With that, you now have a server with a strong security foundation that will give you peace of mind knowing that your server is protected. You may now proceed to build your platform according to your needs. Thank you for following along, and feel free to check back with us for further updates.
Learn more about our VPS hosting services and VPS hosting price.
* This post is for informational purposes only and does not constitute professional, legal, financial, or technical advice. Each situation is unique and may require guidance from a qualified professional.
Readers should conduct their own due diligence before making any decisions.