Table of Contents
- What is HIPAA Compliance?
- Why is HIPAA compliance required?
- 2026 Adjusted Penalty Table
- 10-Step HIPAA Compliance Checklist
- Step #1 – Create a Security and Privacy Policy
- Step #2 – Name a Privacy and Security Officer
- Step #3 – Risk Analysis + Vulnerability Management
- Step #4 – Create a Specific Policy for Email
- Step #5 – Create a Specific Mobile Policy
- Step #6 – Train Your Staff
- Step #7 – Update Your Notice of Privacy Practices (NPP)
- Step #8 – Solidify Business Associate Relationships
- Step #9 – Establish a Protocol for Possible Breaches
- Step #10 – Evidence and Enforcement
- FAQ
- Conclusion
Becoming HIPAA compliant means you build and run a program that protects PHI (and especially ePHI) using the HIPAA Privacy, Security, and Breach Notification Rules. There is no official HIPAA certification; instead, you demonstrate compliance through written policies, workforce training, signed vendor agreements (BAAs), and technical safeguards, supported by ongoing documentation.
Having a quick, clear, and easy 10-step HIPAA compliance checklist to run through can be a major help, which is what we are doing here. We will also take a look at a series of hosting questions from an Atlantic.Net healthcare client interested in learning more about compliance specifics.
What is HIPAA Compliance?
HIPAA compliance is an operating state; it’s not a badge, and you don’t “buy” compliance from a tool or a hosting provider. Vendors instead support your compliance program, but you still own policies, access decisions, training, and breach response.
If you handle electronic protected health information (ePHI), the HIPAA Security Rule requires administrative, physical, and technical safeguards tailored to your risks.
Why is HIPAA compliance required?
The HHS recently updated the civil monetary penalties for HIPAA violations. Effective January 28, 2026, these adjusted values reflect a cost-of-living increase to account for inflation.
Violation Tiers: The penalty structure remains divided into four tiers based on your level of knowledge and intent.
- Tier 1 (Lack of Knowledge): The entity did not know and could not have known of the violation.
- Tier 2 (Reasonable Cause): The entity knew or should have known, but did not act with willful neglect.
- Tier 3 (Willful Neglect – Corrected): The violation was due to intentional neglect but was fixed within 30 days of discovery.
- Tier 4 (Willful Neglect – Not Corrected): The violation was due to intentional neglect and was not fixed within 30 days.
2026 Adjusted Penalty Table
These figures apply to penalties assessed on or after January 28, 2026, for violations occurring after November 2, 2015.
| Penalty Tier | Culpability Level | Minimum (Per Violation) | Maximum (Per Violation) | Annual Cap (Identical Violations) |
| Tier 1 | Lack of Knowledge | $145 | $73,011 | $2,190,294 |
| Tier 2 | Reasonable Cause | $1,461 | $73,011 | $2,190,294 |
| Tier 3 | Willful Neglect (Corrected) | $14,602 | $73,011 | $2,190,294 |
| Tier 4 | Willful Neglect (Uncorrected) | $73,011 | $2,190,294 | $2,190,294 |
Note on Enforcement Discretion: While these are the official inflation-adjusted figures, OCR has previously applied “enforcement discretion” to lower the annual caps for Tiers 1, 2, and 3. However, the legal maximums remain at the higher levels shown above, and Tier 4 violations always carry the highest financial risk.
Administrative Simplification: Beyond data breaches, these penalties also apply to other HIPAA rules, such as failing to provide a Summary of Benefits and Coverage (SBC), which now carries a maximum penalty of $1,443 per failure.
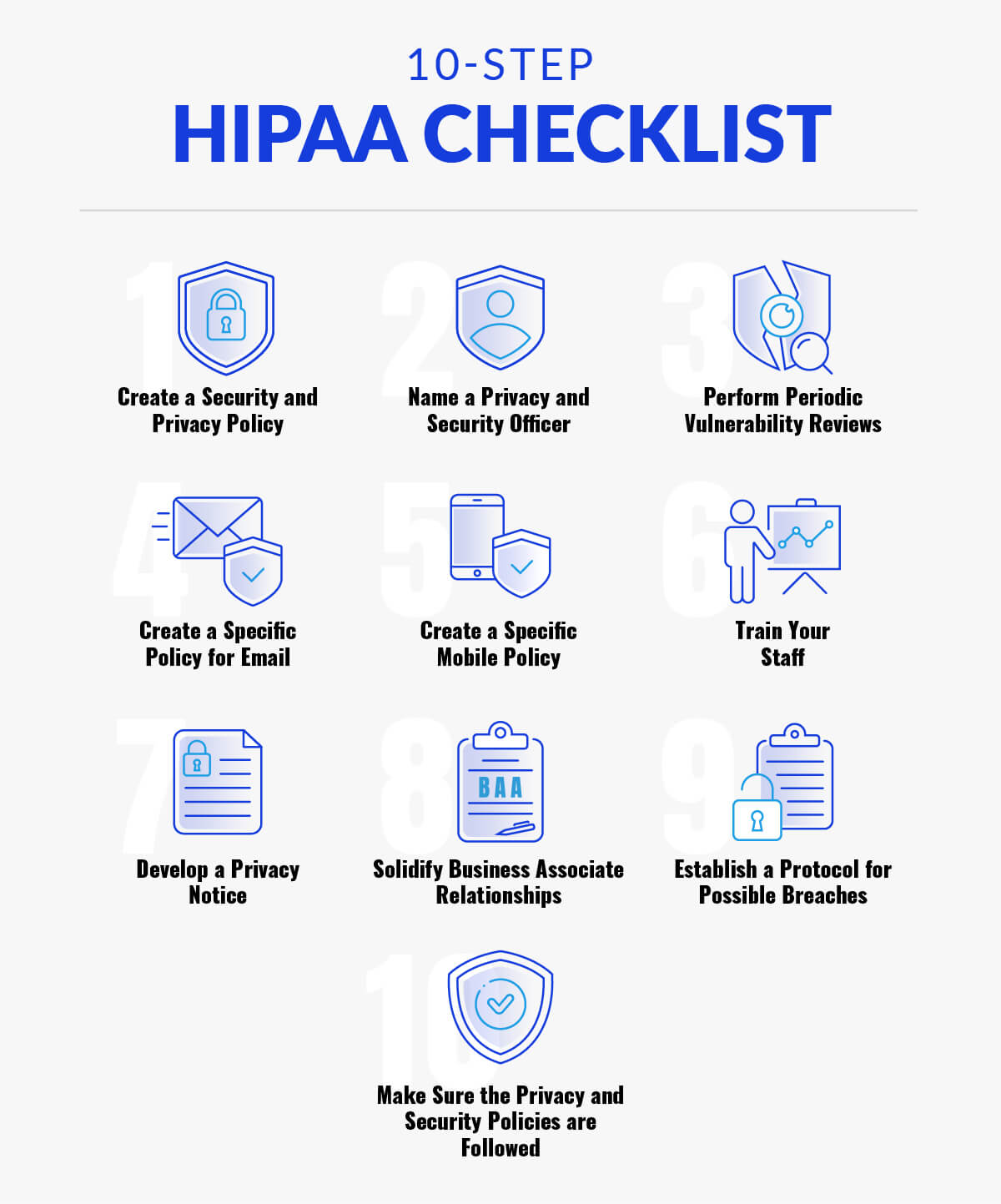
10-Step HIPAA Compliance Checklist
Maintaining compliance in 2026 requires more than just a checklist; it requires a proactive partnership with your infrastructure provider. At Atlantic.Net, we ensure our HIPAA-compliant hosting solutions align with the latest federal requirements, including the February 16, 2026, deadline for updated privacy notices. To begin, you must understand electronic Protected Health Information (ePHI), which refers to any PHI that is covered by HIPAA security regulations and is produced, saved, transferred, or received in an electronic form.

Step #1 – Create a Security and Privacy Policy
A security and privacy policy is a controlled set of documents mapping directly to your safeguards and workflows. We recommend including:
- Scope and Definitions: Define ePHI vs. PHI, systems in scope, and “minimum necessary” access.
- Administrative Safeguards: Document your risk management process and security incident procedures.
- Technical Safeguards: Define MFA policies, audit logging, and encryption standards.
- Physical Safeguards: Control facility access and device disposal.
- Cloud/Shared-Responsibility Appendix: Clearly state who secures specific layers of the IaaS/SaaS stack.
Tracking-Tech Policy: Address the use of pixels and cookies on authenticated pages, as OCR guidance confirms these generally have access to ePHI.

Step #2 – Name a Privacy and Security Officer
These roles require defined authority and budget influence.
- Privacy Officer: Focuses on policy ownership, HIPAA Business Associate Agreements (BAAs), and patient rights.
- Security Officer: Manages the risk analysis program and incident response.
Note: You must establish a HIPAA Business Associate Agreement (BAA) with all relevant vendors.

Step #3 – Risk Analysis + Vulnerability Management
NIST SP 800-66 Rev. 2 provides the current implementation guidance for these assessments.
- Security Risk Analysis: Map where ePHI is created and stored. Identify threats like ransomware pathways.
- Vulnerability Management: Perform authenticated scanning and patch management with remediation SLAs.
Configuration Integrity: Use CIS baselines to detect configuration drift.

Step #4 – Create a Specific Policy for Email
Encryption for ePHI is an “addressable” specification, meaning you must implement it or provide a documented, reasonable alternative.
- TLS Standards: All emails containing ePHI must use TLS 1.2 or 1.3 for data in transit. Avoid outdated SSL terminology.
Approved Systems: Use secure messaging portals to ensure your email system is HIPAA compliant rather than standard unencrypted email unless the patient is warned of the risk and explicitly consents.

Step #5 – Create a Specific Mobile Policy
Mobile devices are primary ePHI pathways. Your policy must cover:
- Device Management: Use Mobile Device Management (MDM) for remote wipes, encryption at rest, and screen locks.
Storage Restrictions: Prohibit ePHI storage in personal cloud backups or consumer messaging apps.

Step #6 – Train Your Staff
Training should be continuous.
- Modules: Use short, quarterly “micro” modules in addition to annual refreshers.
Phishing Simulations: Track and remediate repeat failures to reduce the risk of credential theft.

Step #7 – Update Your Notice of Privacy Practices (NPP)
Compliance with updated NPP requirements is mandatory by February 16, 2026.
- 42 CFR Part 2: Your NPP must now include specific language regarding the confidentiality of Substance Use Disorder (SUD) treatment records.
Redistribution: Ensure the updated NPP is posted on your website and available at all points of service.

Step #8 – Solidify Business Associate Relationships
This is a frequent failure point.
- Vendor Inventory: Identify all vendors that touch ePHI.
BAA Execution: Ensure a signed BAA is in place before any data is shared. Atlantic.Net provides a BAA for all our HIPAA-compliant customers.

Step #9 – Establish a Protocol for Possible Breaches
Your plan must include a HIPAA four-factor risk assessment to determine if an incident is a reportable breach:
- The nature and extent of the ePHI involved.
- The unauthorized person who used the information.
- Whether the information was actually acquired or viewed.
- The extent to which the risk has been mitigated.

Step #10 – Evidence and Enforcement
OCR audits now focus heavily on “recognized security practices.”
- Audit Logs: Regularly review logs for unauthorized access to ePHI.
- Policy Attestation: Require annual workforce sign-offs on all privacy and security policies.
Immutable Backups: Maintain offline or immutable backups to ensure resilience against ransomware.

FAQ
Is there a HIPAA certification?
No official government “HIPAA certification” exists. You demonstrate compliance through policies, safeguards, training, BAAs, and documentation that you can defend during audits and investigations.
How often should we do a HIPAA risk analysis?
HIPAA doesn’t set a single calendar interval, but risk analysis must be accurate and thorough, and you should update it when systems, vendors, workflows, or threats change. Treat it as continuous program work, not a one-time report.
Does HIPAA require encryption?
Encryption is “addressable” in key Security Rule specifications. If encryption is reasonable and appropriate based on your risk analysis, implement it. If not, implement an equivalent alternative or document why neither is reasonable and appropriate.
Can we use cloud services for ePHI?
Yes—if you sign a HIPAA-compliant BAA with the cloud service provider and otherwise comply with HIPAA. Cloud does not absolve you of your responsibilities for configuration, access, and governance.
Do we need a BAA with every vendor?
You need a BAA with vendors that create, receive, maintain, or transmit PHI/ePHI on your behalf as a business associate relationship. Not every vendor is a business associate, but you should document your decision either way.
What are the HIPAA breach notification timelines?
HIPAA breach notification generally requires notification without unreasonable delay and, for certain notices, no later than 60 days after discovery. HHS also publishes instructions for reporting breaches to the Secretary.
Covered entity vs business associate: what changes?
Covered entities have direct obligations, such as issuing a Notice of Privacy Practices. Business associates must comply with Security Rule requirements for ePHI, meet Privacy Rule limits through contract, and report breaches to covered entities under the Breach Notification Rule.
Conclusion
Every healthcare company must ask for advice when they work with IT providers since any issues with the provider would pose a risk to their patient’s health information. After all, even going through a minor HIPAA violation can be disastrous to a healthcare IT organization.
Atlantic.Net is a trusted HIT provider. Our clients trust us because we are experts on the subject and are fully transparent in all communications, as evidenced by this customer testimonial below: “Atlantic.Net’s reputation for 100% up-time, their secure infrastructure, and expertise in Healthcare IT were key components in finalizing our partnership,” said Complete Healthcare Solutions Vice President Joseph Nompleggi.
Feel free to contact us today to see if we can help you meet your HIPAA compliance needs with any of our award-winning HIPAA-Compliant Hosting or Dedicated Hosting.
Read More About HIPAA Compliance
- HIPAA Compliance Checklist
- What Is the HIPAA Security Rule?
- Top Considerations for HIPAA File Storage
- HIPAA Data Storage Requirements
- Protecting e-PHI in the Cloud
- What Is HIPAA Cloud Computing?
- What Is Healthcare Hosting?
- What Is PHI?
This article updated with the latest information on April 24, 2026.

* This post is for informational purposes only and does not constitute professional, legal, financial, or technical advice. Each situation is unique and may require guidance from a qualified professional.
Readers should conduct their own due diligence before making any decisions.